Data breach lawsuits are becoming a serious concern for small businesses in 2026. A single cyberattack can trigger far more than temporary disruption. It can lead to customer complaints, regulatory scrutiny, lost revenue, and civil claims from people whose personal data was exposed. For small companies that already operate with limited staff and tighter budgets, even one lawsuit may create long-term operational and financial pressure.
Many owners assume cyber lawsuits mainly affect giant corporations, but that assumption can create costly blind spots. Smaller companies often collect customer names, addresses, payment details, login credentials, health information, or employee records. When that data is exposed, stolen, or mishandled, the business may face legal claims tied to negligence, privacy violations, breach notification failures, or weak cybersecurity practices. As discussed in Cybersecurity and Privacy Law: Protecting Your Digital Rights in California, privacy expectations and legal standards are becoming more visible to businesses and consumers alike.
Why Data Breach Lawsuits Are Rising in 2026
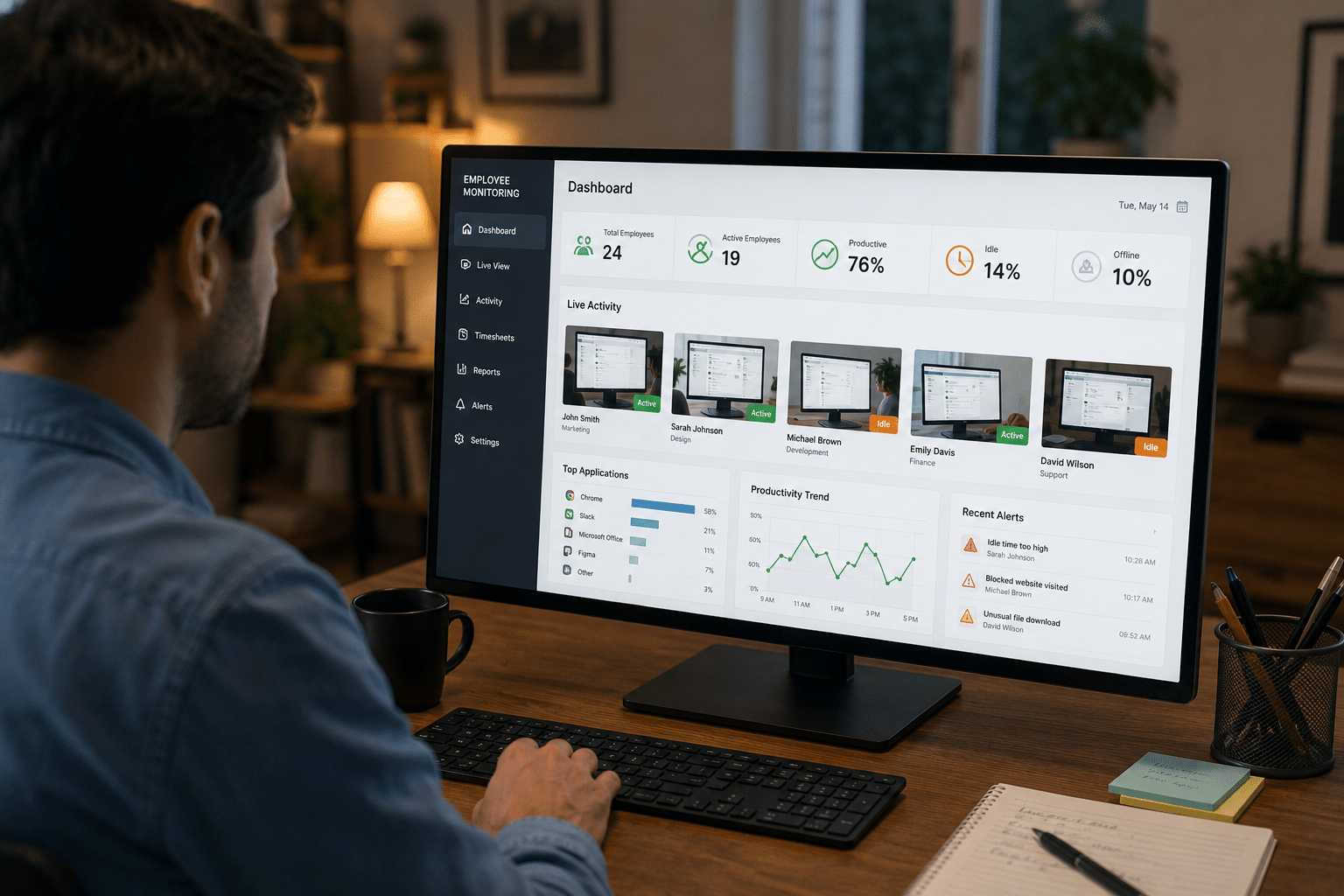
 Data breach litigation is growing because digital risk is now part of everyday business operations. Small businesses rely on payment processors, cloud tools, CRMs, email platforms, remote access systems, and AI-enabled software to serve customers. Each tool may improve efficiency, but each one can also create a new point of vulnerability. Attackers know smaller organizations sometimes lack mature security controls, dedicated IT teams, or incident response planning.
Data breach litigation is growing because digital risk is now part of everyday business operations. Small businesses rely on payment processors, cloud tools, CRMs, email platforms, remote access systems, and AI-enabled software to serve customers. Each tool may improve efficiency, but each one can also create a new point of vulnerability. Attackers know smaller organizations sometimes lack mature security controls, dedicated IT teams, or incident response planning.
At the same time, state privacy laws, industry regulations, and consumer expectations are becoming more demanding. Customers expect businesses to protect their personal information. Regulators expect companies to detect and report breaches in a timely way. Plaintiffs’ lawyers increasingly examine whether a company ignored warning signs, failed to patch known vulnerabilities, or stored sensitive data longer than necessary. Businesses that are already exploring newer systems may also benefit from reviewing how advanced AI risk controls are becoming mandatory in law firms, since AI governance and cybersecurity oversight are becoming closely connected.
Common Events That Trigger Lawsuits
A lawsuit may follow many types of incidents, not just a massive hack that makes headlines. Small businesses may be sued after ransomware attacks, phishing compromises, lost devices, exposed cloud storage, employee mistakes, weak password practices, or vendor-related failures. In some cases, the company may not even realize a breach occurred until customers report identity theft, fraudulent transactions, or suspicious account activity.
Claims often become more likely when the exposed data includes Social Security numbers, financial account information, driver’s license numbers, health data, tax records, or sensitive employee records. Even if the business did not intend to harm anyone, plaintiffs may argue that poor security, delayed notice, or weak internal controls caused preventable damage.
What Plaintiffs Usually Claim After a Breach
After a breach, customers, employees, or business partners may bring claims based on negligence, invasion of privacy, breach of contract, breach of implied contract, unfair business practices, or failure to protect confidential information. The exact claims depend on the facts, the type of data involved, and the laws that apply in the state where the incident occurred. Some lawsuits focus on actual fraud losses, while others focus on time spent monitoring accounts, replacing cards, repairing credit, or dealing with identity theft concerns.
Plaintiffs may also argue that the business made promises in its privacy policy, user agreement, employee handbook, or security statements that it did not actually follow. If a company claimed to use strong safeguards but failed to encrypt data, enforce access controls, or properly train staff, those statements may become part of the dispute. The Federal Trade Commission has repeatedly emphasized the importance of truthful data security representations and reasonable safeguards. Businesses can review FTC guidance here: FTC privacy and security guidance.
Why Even a Small Lawsuit Can Hurt a Small Business
A data breach lawsuit does not need to result in a massive verdict to damage a small company. Legal fees, forensic investigations, breach notifications, customer support costs, downtime, vendor remediation, insurance disputes, and reputation loss can pile up quickly. A business may spend months answering questions from attorneys, insurers, regulators, customers, and payment partners while also trying to keep normal operations running.
For many owners, the hidden cost is distraction. A company that should be focused on growth, service, hiring, and customer retention may instead spend weeks managing document preservation, evidence collection, and emergency technical fixes. This is one reason businesses should avoid a reactive mindset. Many of the same habits that reduce litigation risk also support better operations overall.
How Courts and Regulators Look at Business Conduct
When a breach leads to legal action, the central question often becomes whether the business acted reasonably before and after the incident. Courts and regulators may look at whether the company used multi-factor authentication, updated software, limited access to sensitive data, monitored systems, kept logs, trained employees, used secure vendors, and followed its own written policies. They may also review how quickly the company detected the problem, whether it investigated thoroughly, and whether notice was given on time.
This does not mean every breached company automatically did something wrong. Cyberattacks can still affect diligent organizations. But if the evidence shows preventable gaps, outdated systems, ignored alerts, or poor documentation, the company’s defense becomes harder. The Cybersecurity and Infrastructure Security Agency offers practical guidance businesses can use to improve their posture before an incident happens: CISA cybersecurity best practices.
The Role of Privacy Laws and Notification Rules
 State breach notification laws continue to shape how businesses respond after an incident. A company may have to notify affected individuals, consumer reporting agencies, state agencies, or other parties depending on the number of people affected and the kind of data exposed. In California, privacy requirements are especially important, which is why content like Cybersecurity and Privacy Law: Protecting Your Digital Rights in California may be useful for businesses trying to understand the broader privacy landscape.
State breach notification laws continue to shape how businesses respond after an incident. A company may have to notify affected individuals, consumer reporting agencies, state agencies, or other parties depending on the number of people affected and the kind of data exposed. In California, privacy requirements are especially important, which is why content like Cybersecurity and Privacy Law: Protecting Your Digital Rights in California may be useful for businesses trying to understand the broader privacy landscape.
If health information is involved, federal healthcare privacy requirements may also come into play. If payment card data is compromised, card brand rules and PCI obligations may create additional exposure. The U.S. Department of Health and Human Services provides breach and HIPAA resources here: HHS HIPAA security resources. Payment security standards are available through the PCI Security Standards Council: PCI Security Standards Council.
Practical Ways to Reduce Lawsuit Risk
Small businesses cannot eliminate cyber risk entirely, but they can reduce their exposure. Start by identifying what personal or sensitive data the business collects, where it is stored, who can access it, and how long it is retained. Many companies hold more data than they need. Data minimization can shrink the damage caused by a breach and may also make compliance easier.
Next, improve basic cyber hygiene. Use multi-factor authentication, strong password policies, timely patching, encrypted devices, secure backups, limited admin rights, and vendor review procedures. Employee training also matters because phishing and social engineering remain common entry points. A short, recurring training program is usually more effective than one annual session that everyone forgets.
Written policies are equally important. If a lawsuit arises, good documentation may help show the business took security seriously. Incident response plans, access control policies, vendor agreements, retention schedules, employee training records, and breach response checklists may all become valuable later. Businesses should also review internal operations for broader legal gaps. Many avoidable problems appear long before litigation starts, which makes Common Legal Mistakes to Avoid a useful related read for owners trying to strengthen their overall legal footing.
Vendor Risk Is Business Risk
Many data breaches trace back to third parties such as payroll providers, email vendors, marketing tools, managed service providers, or cloud software companies. A small business may believe outsourced systems transfer the security burden, but customers and regulators may still look to the business that collected the data in the first place. That means vendor contracts, security questionnaires, and access limitations matter.
Before onboarding a vendor, businesses should ask what data the vendor will access, how that data is protected, whether encryption is used, what happens during an incident, and whether subcontractors are involved. Contracts should clearly address security responsibilities, incident notice timelines, and cooperation obligations if an investigation occurs.
Insurance Can Help, but It Is Not a Complete Solution
Cyber insurance may soften the financial impact of a breach, but owners should not assume every loss or lawsuit will be fully covered. Policies vary widely. Some cover forensic costs, response services, and legal defense, while others include exclusions tied to weak controls, delayed reporting, vendor incidents, or certain kinds of fraud. Business owners should review their policies carefully and ask how claims are handled after a data incident.
Understanding costs before a problem happens is part of smarter legal planning. That same mindset also appears in Understanding Legal Fees: What You’ll Really Pay for a Lawyer in 2025, which can help readers think more clearly about legal expenses before they are under pressure.
What to Do Right After a Breach
If a breach happens, speed and structure matter. The business should secure affected systems, preserve evidence, involve legal counsel, coordinate with IT or forensic professionals, review notification duties, and avoid making public statements before the facts are clear. Careless early messaging can create legal problems later if it turns out the company overstated or understated what happened.
Internal records should be preserved immediately, including logs, emails, alerts, tickets, vendor messages, and security snapshots. If the incident may involve criminal conduct, law enforcement coordination may also become appropriate. The U.S. Small Business Administration offers cybersecurity resources for smaller organizations here: SBA cybersecurity guidance for small businesses.
Final Thoughts
Data breach lawsuits are no longer a remote issue for small businesses. In 2026, they are part of the real legal risk surrounding digital operations, customer data, vendor management, and business growth. The businesses in the strongest position are usually not the ones with unlimited budgets. They are the ones that understand what data they hold, apply practical security controls, document their decisions, review vendors carefully, and respond quickly when something goes wrong.
Small business owners do not need to panic, but they do need to treat cybersecurity as a legal and operational priority. A stronger privacy and security posture may reduce the chance of a breach, improve response when one occurs, and place the business in a better position if claims follow. In a legal environment where digital trust matters more each year, preparedness can make a major difference.